Digitalization has prompted business owners to connect their devices and systems. This has given their physical assets digital profiles so that they can extract data from the edge and send it to the control center, where they can analyze data or develop applications. In this scenario, systems that were previously air-gapped become interconnected, which exposes them to cybersecurity threats. As the number of cybersecurity incidents continues to grow annually, business owners have started to think about how to embark on their industrial cybersecurity journey. Although there are many standards, frameworks, and guidelines for cybersecurity, we shall focus on what is considered by many to be the three most important points regarding cybersecurity: building visibility for your network and security status, activating network segmentation, and securing your critical assets.
We will start by looking at how to enhance network visibility when performing configurations, operations, as well as how to respond to incidents and maintain the security of your network.
▎Configuration ▎
Follow Security Setting Guidelines and Visualize the Status of Your Network
In our daily life, we often see media reports stating how surprisingly easy it is to hack an IP camera if the default password has not been changed. Thus, we are encouraged to regularly update our passwords and embrace other security features such as two-factor authentication to ensure we maintain good cyber hygiene. The same logic applies to industrial applications. A cybersecurity threat arises when the default password of industrial devices is not changed, or the devices are used without sufficient protection. As more devices are becoming interconnected at production sites, this risk that one device becomes corrupted and allows an attacker access to the entire network is growing exponentially. If you want to have a better understanding of how to keep your industrial devices secure by adhering to the recommended security settings, you can refer to our security hardening guide.
To ensure industrial control systems have the appropriate cybersecurity protection, a long and often complex list of configurations must be performed. One of the most effective methods to simplify this task is to use a network management software that allows you to quickly visualize the security status and security parameters. Felipe Sabino Costa, whose current roles include ISA cybersecurity instructor and Moxa LATAM Industrial Cybersecurity expert, explained in this white paper, A Systematic Approach to Checking Cybersecurity, that a systematic and automatic approach to security configurations, with a focus on network assets, significantly decreases the probability of implementing incorrect or incomplete configurations that can occur when configurations are entered manually.
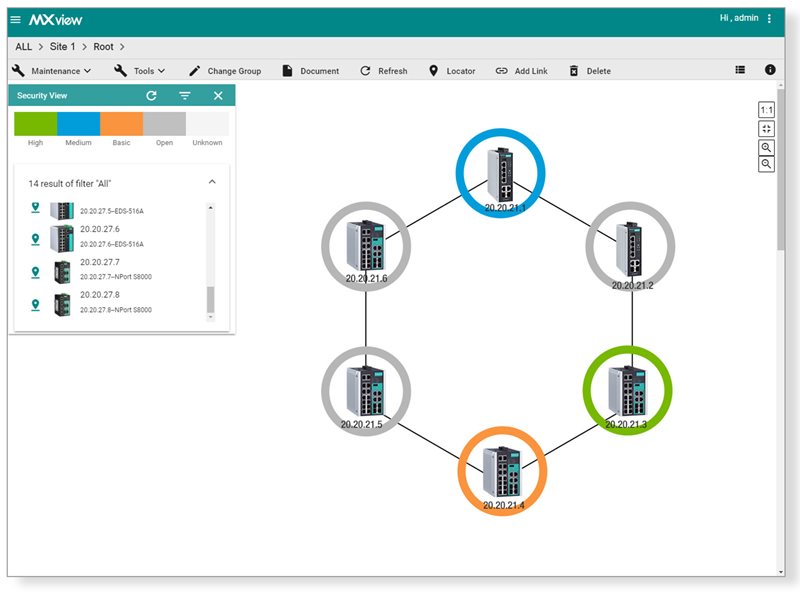
Visualizing the security status of networking devices by using different colors.
When everything has been set up, network administrators can easily check the dashboard to see if anything needs to be updated to ensure operations remain smooth and secure.
▎Operation ▎
Enhance Visibility of Your Industrial Networks
Although digitalization has allowed people, machines, and systems to become interconnected, it has unfortunately increased the possibility of introducing cybersecurity threats into the network. Therefore, for all activity on your network, it is essential to understand the real-time status of your assets. There are several ways to achieve this goal. First, dashboards and topologies that display network and security activities in real time are very helpful for network administrators or security officers who need to collect the latest information and view it quickly. Second, it is important to keep event logs so that administrators can ascertain when incidents occurred. Third, a regular backup mechanism is very helpful if the network needs to be restored to a specific point in time.
Watch the video to learn how to visualize industrial networks.
Visualizing your network allows you to gain a better understanding of how your network is currently grouped together. In fact, one of Moxa’s customers wanted to use network segmentation to enforce cybersecurity policies. This task was made easier for them as they already had an overview of their network topology. Typically, within any plant, there will be a very large number of devices. Therefore, having an overview of the network topology will allow you to design the network and maximize the effectiveness of your cybersecurity. Download the case studies to learn more.
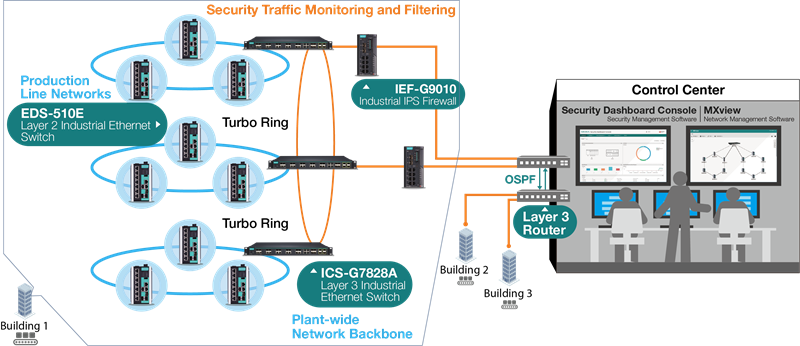
A real case of network segmentation done properly that helped customers implement cybersecurity policies.
Download the case studies.
▎Response and Maintenance ▎
Centralized Security Management Increases Response Times
As cybersecurity threats are constantly evolving, network owners must remember that cybersecurity is a task that will never be completed. Industrial networks need to be constantly monitored, maintained, and updated to ensure that the system and devices have sufficient protection. When engineers have finished setting up their network, they should collect data and determine what is considered normal activity for their network. By using this information as a baseline, administrators can observe if any abnormal activity happens on the network. The common approach in the industry is to construct dashboards to record network events, using either pie charts or bar charts. This allows operators to quickly identify if there is any abnormal or potentially dangerous activity on the network and to start looking for potential causes. Adopting this approach effectively increases the ability of the team to respond to incidents. As we mentioned earlier, the more devices that are installed on a network, the more difficult it becomes to ensure that all devices have the most up to date security policies applied. An efficient way to lessen the heavy loading of this task and reduce the likelihood that errors occur, is for administrators to allow cybersecurity policies and pattern updates to be performed in groups.
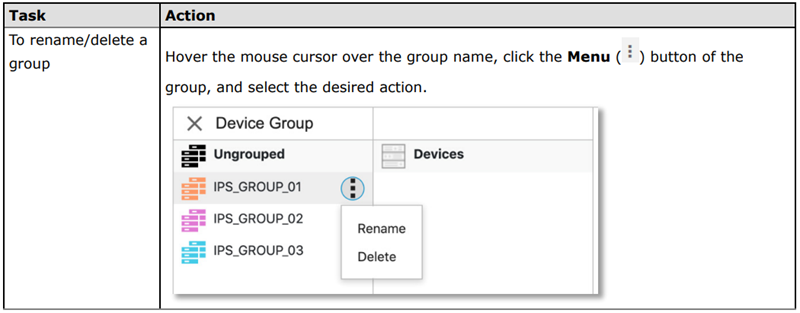
Updating patterns and enabling cybersecurity policies for a batch of devices.
Ensuring robust cybersecurity on industrial networks is a complex issue that requires comprehensive solutions. Since there is no silver bullet, we highly recommend that business owners and network administrators start from the three fundamental aspects mentioned in this article to strengthen their cybersecurity. Throughout this process, it is important to remember to utilize secure network infrastructure that connects and enables your business operations and to protect your critical assets from cyberattacks such as ransomware. How should you begin this journey? Start from building the visibility of your industrial networks. You can learn more about how to achieve this from our cybersecurity website www.moxa.com/Security.
Please visit the product pages to learn more information about MXview network management software and Security Dashboard Console security management software.