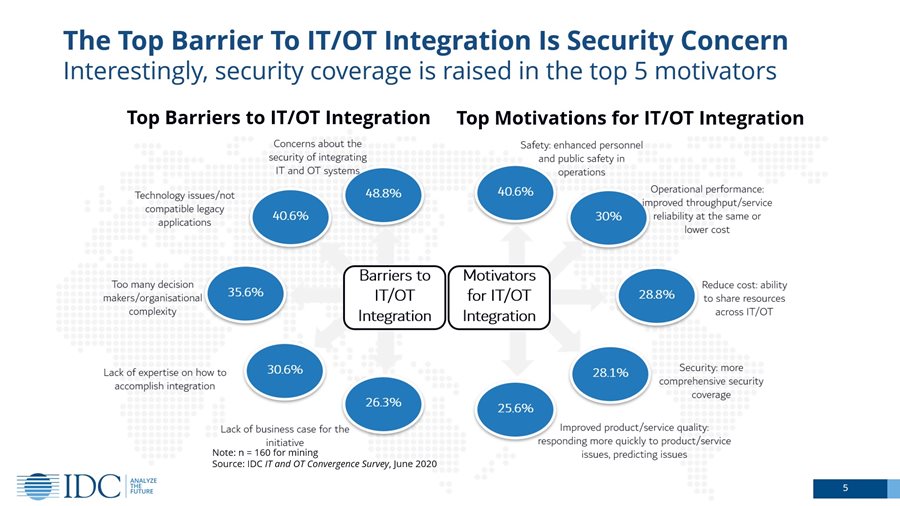
With increasing demands on OT/IT integration, data security is at the forefront of our concerns more than ever. In fact, according to an IDC survey, security is considered the top barrier to OT/IT integration. At the same time, it is also considered a top-five motivator, meaning enhanced OT security is one of the means to bring about successful OT/IT integration. However, when integrating OT and IT systems from traditionally closed to open data systems, unwanted access may be given to an organization’s private operation data.
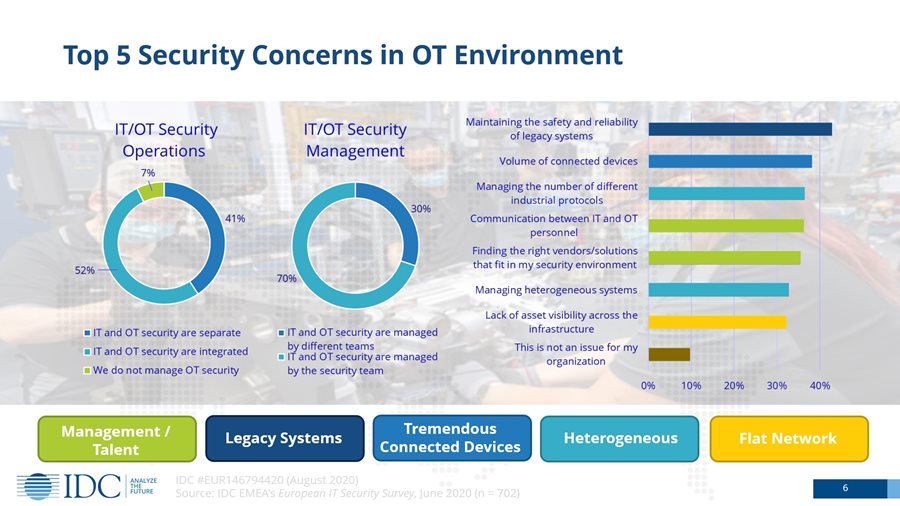
“If we look closer to why security is the largest barrier, we will find that in the OT environment one of the top security concerns is maintaining legacy systems safely and reliably,” said Helen Chiang, general manager at IDC Taiwan, in the Security Talks Show. “On an OT site, you’ll find many legacy systems and applications. They are not only isolated but also agentless, meaning the asset has limited resources to run the security solution that we usually execute in an IT environment.”
To connect unconnected legacy systems, several steps can be taken to enhance connectivity security and reduce security concerns for your OT/IT integration projects.
Tip 1: Change default passwords for your networking devices
Because your legacy systems are connected through networking devices, the first thing you can do to enhance connectivity security is to replace default passwords. The security strength of default passwords is usually low and easy to find in a public user manual. Don’t take this risk when you can easily prevent it.
Tip 2: Disable unused yet connected ports and services
When you deploy a networking device, some unused ports or unnecessary services may open the door to cyberthreats in your application. You can disable these ports and services to block the available paths to unwanted access.
Tip 3: Verify firmware source before update
When your networking devices require firmware update, make sure you have a mechanism to verify the firmware source. Checking the CRC code is one way to ensure the firmware you are about to use comes from the original source. Another way to verify the firmware source is through secure boot design. It’s a feature that ensures the integrity of firmware running on your platform.
Tip 4: Use secure communication protocols
It’s important to use a secure protocol (i.e., TLS 1.2 support in HTTPS and SNMPv3) for your connected legacy systems. It can reduce the chances of unwanted access while you are managing networking devices, and it can enhance data integrity while you are transmitting data. Also, when you deploy your networking devices, disable unsecure protocols to minimize the chances of a manual error.
Tip 5: Only allow authorized users to access your devices and network
Prioritize your critical assets and validate network segmentation. Then, you will have a clearer picture about what authority can be granted to what specific segment. Furthermore, deploy trust-listing such as listing only permitted IP addresses to keep unwanted access out of your legacy systems. Other advanced functions are also available to limit unwanted access. For example, you can define a specific protocol format or command that can access your devices and network.
Tip 6: Encrypt critical data before transmissions
In OT environments, critical data leakage can cause operation downtime, thus impacting operational efficiency. For connected legacy systems, you can encrypt critical data during transmissions to enhance your data confidentiality and reduce the chances of negatively impacting your daily operation.
Tip 7: Constantly monitor if your networking devices are at your desired security level
When you get your legacy systems connected, you should define the security measures based on your application’s demands so that you can easily monitor and manage your networking devices. When the system networks are up and running, constantly monitor whether the security status of your devices meets the requirements you defined from the onset.
Tip 8: Periodically scan vulnerabilities for potential threats
It’s essential to know what potential threats your legacy systems are facing. Scheduling a vulnerability scan periodically gives you a better idea of the security status of the overall system, helping you to take necessary actions when needed.
Tip 9: Perform security patches for your networking devices to reduce vulnerabilities
We all know that security patching is important. However, it is not always so easy in field sites. From a business perspective, it can lead to tremendous costs when you pause operations to test and perform patches. On the other hand, risks and costs are also involved when you are doing nothing about it. A more sustainable approach is finding a balance midway by performing acceptable batches of security patching for critical field systems.
Tip 10: Use virtual patching for known vulnerability of your legacy systems
In certain situations, security patching is not always an option. Furthermore, some legacy systems are not able to perform patching. For these type of situations, virtual patching is an efficient alternative. You can deploy the virtual patch in the network connected to your legacy systems to eliminate known vulnerabilities and protect the devices against certain exploits. Virtual patching is also a good way to reserve a buffer time while the system is waiting for the next maintenance period to get patched.
Take the above 10 tips into consideration when connecting your legacy systems—it can help you enhance connectivity security and minimize security threats to your legacy systems. Moxa provides a comprehensive security product portfolio for your edge connectivity security. Visit our website to learn more.
- Looking for secure hardened edge connectivity solutions, visit here.
- Looking for Industrial IPS solutions, visit here.